這個消息從5月19日就傳開了。可以理解為網絡戰的最新發展態勢——借由法律為名的公開化。

From left, Chinese military officers Gu Chunhui, Huang Zhenyu, Sun Kailiang, Wang Dong, and Wen Xinyu have been indicted on cyber espionage charges.
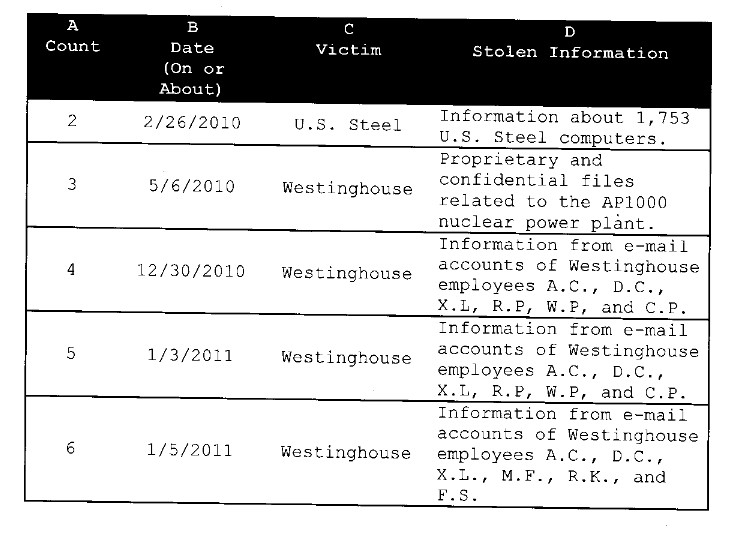
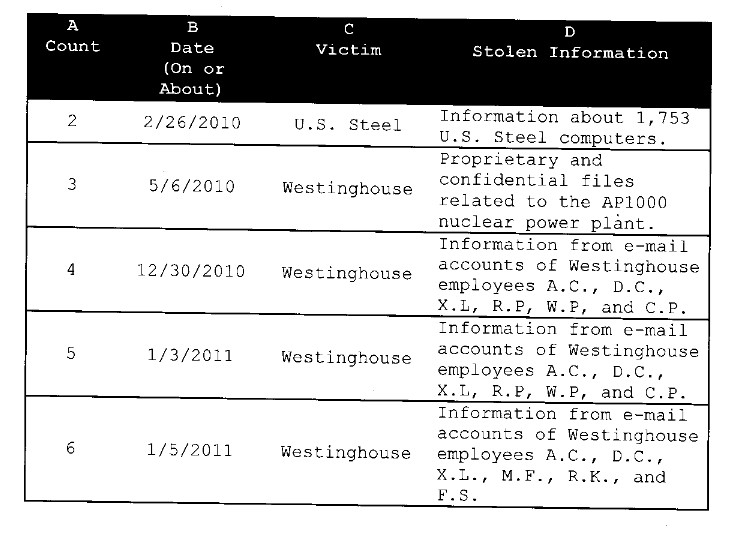
美國司法部認為有必要起訴的理由是認為這個刺探行動超越了他們“給自己劃定”的軍事、政治領域,而將刺探的信息用于經濟目的。在起訴書中大量列舉了受害者的失竊信息,我猜想他們都應該向FBI報案了。
起碼,他們知道他們有什么信息被竊取了,并且通過手段找到了他們認定的犯罪份子。單就這兩點而言,可見美國的信息與網絡安全取證的水平之高。
FBI的新聞稿中寫道:Wang Dong, Sun Kailiang, Wen Xinyu, Huang Zhenyu, and Gu Chunhui, who were officers in Unit 61398 of the Third Department of the Chinese People’s Liberation Army (PLA). The indictment alleges that Wang, Sun, and Wen, among others known and unknown to the grand jury, hacked or attempted to hack into U.S. entities named in the indictment, while Huang and Gu supported their conspiracy by, among other things, managing infrastructure (e.g., domain accounts) used for hacking.
受害人: Westinghouse Electric Co. (Westinghouse); U.S. subsidiaries of SolarWorld AG (SolarWorld); United States Steel Corp. (U.S. Steel); Allegheny Technologies Inc. (ATI); the United Steel, Paper and Forestry, Rubber, Manufacturing, Energy, Allied Industrial and Service Workers International Union (USW); and Alcoa Inc.
刺探的時間跨度: 2006-2014
31條犯罪指控: 31 counts as follow (all defendants are charged in all counts):
|
Count(s) |
Charge |
Statute |
Maximum Penalty |
|
One |
Conspiring to commit computer fraud and abuse
|
18 U.S.C. § 1030(b) |
10 years |
|
Two through nine |
Accessing (or attempting to access) a protected computer without authorization to obtain information for the purpose of commercial advantage and private financial gain |
18 U.S.C. §§ 1030(a)(2)(C), 1030(c)(2)(B)(i)-(iii), and 2 |
Five years (each count) |
|
10-23 |
Transmitting a program, information, code, or command with the intent to cause damage to protected computers |
18 U.S.C. §§ 1030(a)(5)(A), 1030(c)(4)(B), and 2 |
10 years (each count) |
|
24-29 |
Aggravated identity theft |
18 U.S.C. §§ 1028A(a)(1), (b), (c)(4), and 2 |
Two years (mandatory consecutive) |
|
30 |
Economic espionage |
18 U.S.C. §§ 1831(a)(2), (a)(4), and 2 |
15 years |
|
31 |
Trade secret theft |
18 U.S.C. §§ 1832(a)(2), (a)(4), and 2 |
10 years |
Summary of Defendants’ Conduct Alleged in the Indictment
|
Defendant |
Victim |
Criminal Conduct |
|
Sun |
Westinghouse |
In 2010, while Westinghouse was building four AP1000 power plants in China and negotiating other terms of the construction with a Chinese SOE (SOE-1), including technology transfers, Sun stole confidential and proprietary technical and design specifications for pipes, pipe supports, and pipe routing within the AP1000 plant buildings.
Additionally, in 2010 and 2011, while Westinghouse was exploring other business ventures with SOE-1, Sun stole sensitive, non-public, and deliberative e-mails belonging to senior decision-makers responsible for Westinghouse’s business relationship with SOE-1. |
|
Wen |
SolarWorld |
In 2012, at about the same time the Commerce Department found that Chinese solar product manufacturers had “dumped” products into U.S. markets at prices below fair value, Wen and at least one other, unidentified co-conspirator stole thousands of files including information about SolarWorld’s cash flow, manufacturing metrics, production line information, costs, and privileged attorney-client communications relating to ongoing trade litigation, among other things. Such information would have enabled a Chinese competitor to target SolarWorld’s business operations aggressively from a variety of angles. |
|
Wang and Sun |
U.S. Steel |
In 2010, U.S. Steel was participating in trade cases with Chinese steel companies, including one particular state-owned enterprise (SOE-2). Shortly before the scheduled release of a preliminary determination in one such litigation, Sun sent spearphishing e-mails to U.S. Steel employees, some of whom were in a division associated with the litigation. Some of these e-mails resulted in the installation of malware on U.S. Steel computers. Three days later, Wang stole hostnames and descriptions of U.S. Steel computers (including those that controlled physical access to company facilities and mobile device access to company networks). Wang thereafter took steps to identify and exploit vulnerable servers on that list. |
|
Wen |
ATI |
In 2012, ATI was engaged in a joint venture with SOE-2, competed with SOE-2, and was involved in a trade dispute with SOE-2. In April of that year, Wen gained access to ATI’s network and stole network credentials for virtually every ATI employee. |
|
Wen |
USW |
In 2012, USW was involved in public disputes over Chinese trade practices in at least two industries. At or about the time USW issued public statements regarding those trade disputes and related legislative proposals, Wen stole e-mails from senior USW employees containing sensitive, non-public, and deliberative information about USW strategies, including strategies related to pending trade disputes. USW’s computers continued to beacon to the conspiracy’s infrastructure until at least early 2013. |
|
Sun |
Alcoa |
About three weeks after Alcoa announced a partnership with a Chinese state-owned enterprise (SOE-3) in February 2008, Sun sent a spearphishing e-mail to Alcoa. Thereafter, in or about June 2008, unidentified individuals stole thousands of e-mail messages and attachments from Alcoa’s computers, including internal discussions concerning that transaction. |
|
Huang |
|
Huang facilitated hacking activities by registering and managing domain accounts that his co-conspirators used to hack into U.S. entities. Additionally, between 2006 and at least 2009, Unit 61398 assigned Huang to perform programming work for SOE-2, including the creation of a “secret” database designed to hold corporate “intelligence” about the iron and steel industries, including information about American companies. |
|
Gu |
|
Gu managed domain accounts used to facilitate hacking activities against American entities and also tested spear phishing e-mails in furtherance of the conspiracy. |
撇開政治不談,我好奇的是他們的取證分析技術和方法。
根據指控書和相關材料顯示,有幾點比較有趣:
1)為何那么多起美國政府認定的來自的攻擊都沒有起訴,偏偏這次起訴了呢?原因就在于他們這次認定了攻擊行動獲取的企業機密信息被用于了經濟目的,并提供給了本國的企業,用于獲得競爭優勢。那么,他們是如何具體闡述的呢?他們說,這個部隊的人一方面有組織地對美國企業進行刺探,獲取機密情報信息,另一方面這個部隊的人也為國內的企業提供安全服務,在為客戶提供安全服務的時候,將之前獲取的信息透露給了這些國內企業(主要是幾家SOE——國有企業)。仔細一看,他們還真是分析的很深。
2)在認定是這個部隊的人的時候,用了N種方法互相印證,我猜想用到了之前Mandiant的APT1報告中列舉的那些證據或者類似的、更高級的證據。同時,他們還提到了一個論證,就是發現用于回傳機密數據的動態DNS的網站的流量的周期性波動,具有顯著的早8點到晚5點(中國時間)的波峰特性,而其他時間(還有中午1個小時)則呈現波谷,說這跟中國國有事業單位的上班時間很吻合。在指控書附錄中還貼出了幾幅流量圖。很有意思。
3)在指控書中還比較詳細的枚舉了受害人失竊的信息,細到了具體的主機名,信息類型,甚至個別條目。
看了這些你就明白為什么FireEye要收購Mandiant,檢測威脅很重要,數字取證分析和溯源也很重要啊!結合到一起才NB。